Hi all,
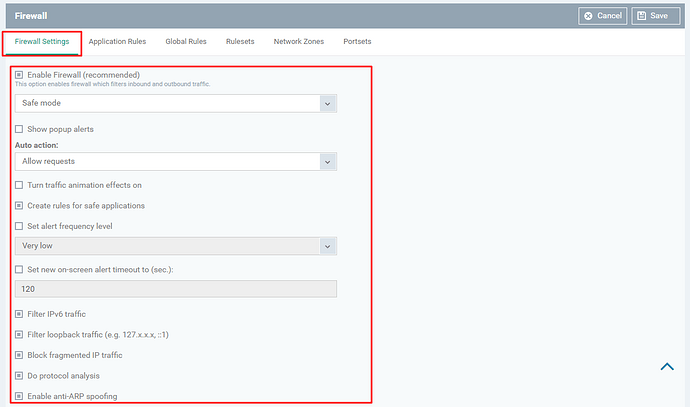
Firewall Settings - Allows the users to set the parameters of Firewall Components
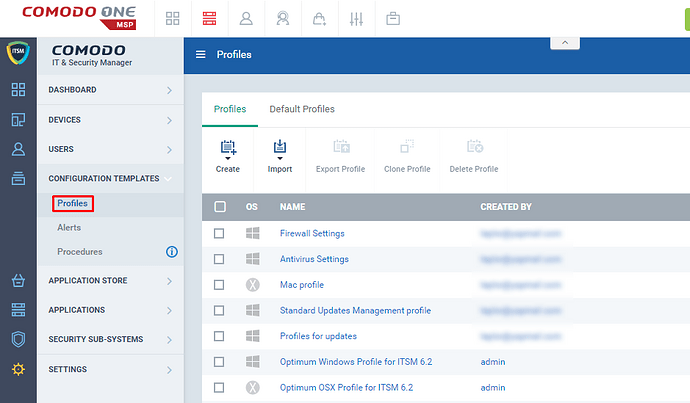
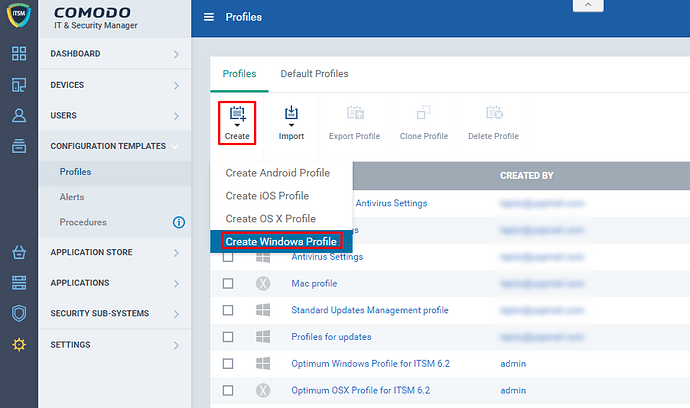
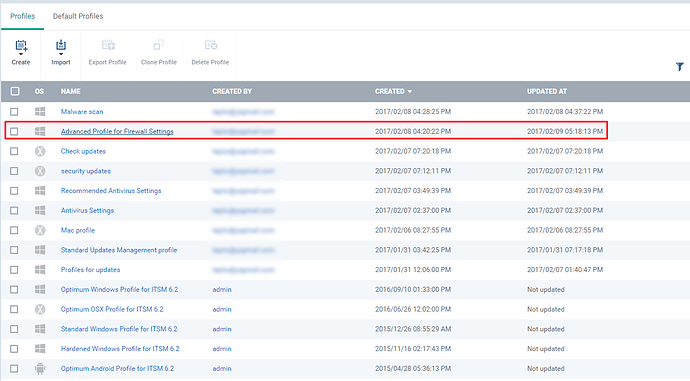
Step [1]: Go to ITSM > CONFIGURATION TEMPLATES > Profiles
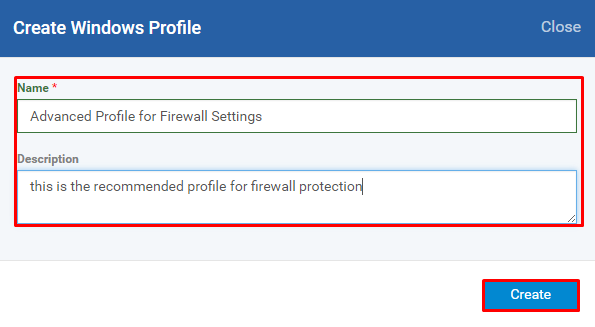
Step [2]: Click Create icon and Choose the Create Windows Profile from the drop down menu
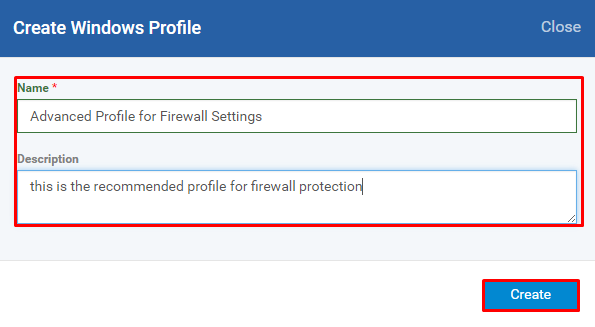
Step [3]: Enter the Name, Description of the profile and Click the Create button
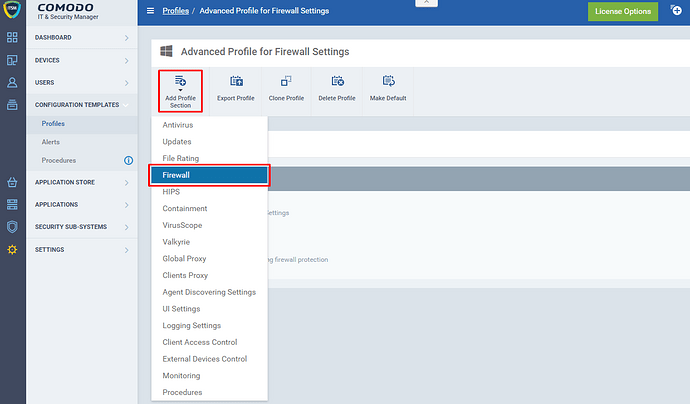
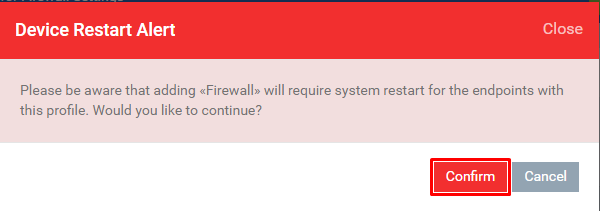
Step [4]: Click Add Profile Section and Choose Firewall from the drop down
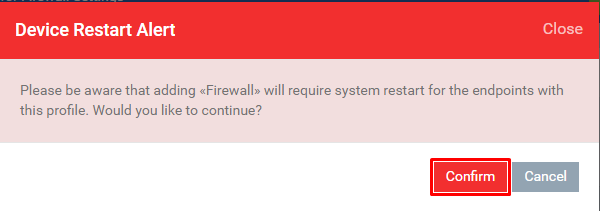
Step [5]: Click the Confirm button
Note:
There are some necessary settings to be completed to continue further on advanced firewall profile such as
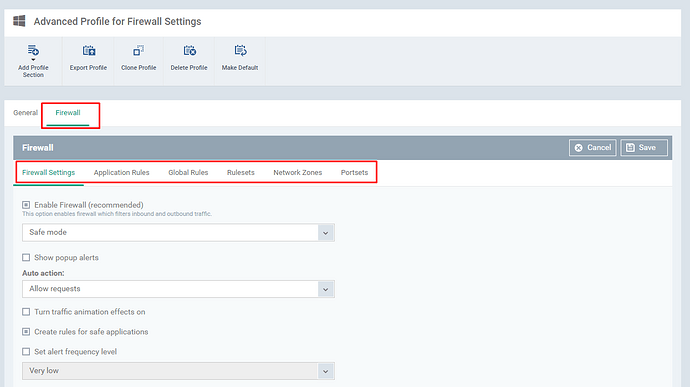
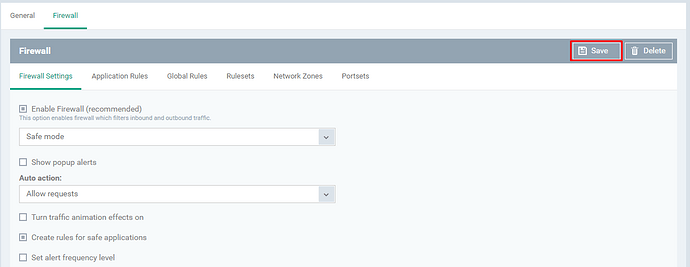
Step [6]: Fill the form loads from Firewall Settings tab
Explanation:
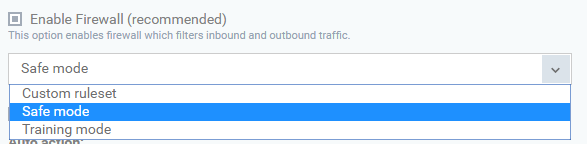
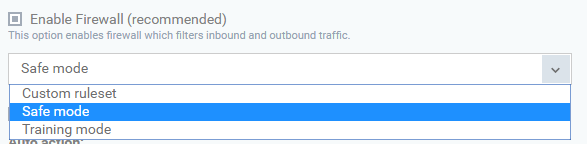
Enable Firewall (recommended) - This option enables firewall which filters inbound and outbound traffic.
- Custom ruleset - Firewall protect the endpoint based on the user rulesets (Described in Application Rules)
- Safe mode - Application access connection based on the Comodo ratings and suppose a new application' access is found then you will be prompted whether trust the application and allow the connection or not.
- Training mode - Automatically creates the ruleset based on the application behavior (Monitors the network connection and resource of the connection)
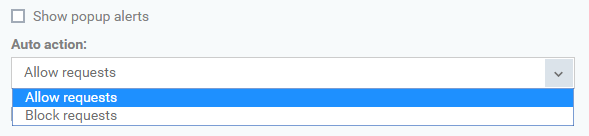
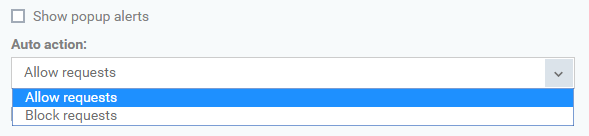
Show popup alerts - You get alerted when the firewall find new request. If you would like to hand over the decision to Comodo then Disable the option and use the “Auto action” option as follows.
Auto action
- Allow Request - Allows requests automatically if the connection is trusted
- Block Request - Blocks requests automatically if the connection is not trusted
Turn traffic animation effects on - CIS on the endpoint displays an animation icon for incoming (yellow down arrow) and outgoing (green up arrow) connection. Hence to the endpoint to do so, you will have to keep the option enabled. If you don't want the effect on the endpoint then disable the option.
Create rules for safe applications - There are three set of activities that are followed by Comodo to rule the application as trusted. The activities are Checks the files at Trusted File list, Checks the vendor at Trusted Software Vendor list, and Constantly Updated Comodo Safelist. Hence CIS start analyzing and reconsider the safe application rules.
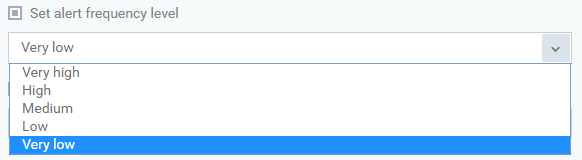
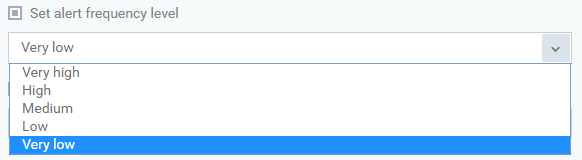
Set alert frequency level - Sets a number of alerts of Comodo generate
- Very High - shows each request individually (separate alerts for outgoing and incoming connection requests for both TCP and UDP protocols on specific ports and for specific IP addresses, for an application)
- High - shows separate alerts for outgoing and incoming connection requests for both TCP and UDP protocols on specific ports for an application
- Medium - shows alerts for outgoing and incoming connection requests for both TCP and UDP protocols for an application
- Low - shows incoming and outgoing connection requests for an application
- Very Low - shows one alert for an application
Set new on-screen alert timeout to (sec.) - Allows to set amount of time the alert should stay on the endpoint
Filter IPv6 traffic - filter IPv6 network traffic
Filter loopback traffic (e.g. 127.x.x.x, ::1) - filter traffic sent through loopback channel (http://localhost)
Block fragmented IP traffic - If the data are larger than the MTU (Maximum Transmission Unit) while transferring b/w two computers then the data are divided into smaller (fragmentation) and which are sent separately.
Hence the packets can create threats and can double the amount of time it takes for single packet transfer and which cause your download speed gets slow down.
Do protocol analysis - checks every packet conforms to that protocols standards
Enable anti-ARP spoofing - If enabled, blocks requests of ARP (Address Resolution Protocol) cache
Step [7]: Click Save button once you have complete the setup on the tab Firewall Settings
Step [8]: Click Profiles menu and check whether the profile has been added to the table.